Abrahasson, Pekka et al.
Agile
software development: Review and Analysis. ESPOO 2002, VTT Publications
478. 107p.
Keywords: Software development, agile processes, agile methods, extreme programming,
agile modelling, open source software development, software project management
Abstract: Agile--denoting "the quality of being agile; readiness for motion,
nimbleness, activity, dexterity in motion"--software development methods are
attempting to offer an answer to the eager business community asking for lighter
weight along with faster and nimbler sofware development processes. This is
especially the case with the rapidly growing and volatile Internet software
industry as well as for the emerging mobile application environment. The new
agile methods have evoked a substantial amount of literature and debates. However,
academic research on the subject is still scarce, as most of existing publications
are written by practitioners or consultants.
The aim of this publication is to begin filling this gap by systematically reviewing
the existing literature on agile sofware development methodologies. This publication
has three purposes. First, it proposes a definition and a classification of
agile software development approaches. Second, it analyses ten sotware development
methods that can be characterized as being "agile" against the defined criteria.
Third, it compares these methods and highlights their similarities and differences.
Based on this analysis, future research needs are identified and discussed.

There are user groups springing
up around the Agile
Alliance focused on improving development processes along the lines of the
Agile Manifesto. I
attended the New
England Agile User Group on Thursday, 18 September, and a good time was
had by all. Ken
Schwaber's comments provide a summary of the meeting.
There is also a new user group in Calgary: Calgary
Agile Methods User Group (CAMUG)

Where do you go to get a
good description of how wireless security works, how it gets hacked, and how
to prevent intrusion? You can go to vendor sites and weed through the hype,
or to hacker sites and sort through dense technical detail. Maybe you just need
a good technical description. Trey "Azariah" Dismukes has written a Wireless
Security Blackpaper that fits the bill.
"While wireless networks have seen widespread adoption in the home user markets,
widely reported and easily exploited holes in the standard security system have
stunted wireless' deployment rate in enterprise environments. While many people
don't know exactly what the weaknesses are, most have accepted the prevailing
wisdom that wireless networks are inherently insecure and nothing can be done
about it. Can wireless networks be deployed securely today? What exactly are
the security holes in the current standard, and how do they work? Where is wireless
security headed in the future? This article attempts to shed light on these
questions and others about wireless networking security in an enterprise environment."
![]()
Note: CMM is a service
mark of the Software Engineering
Institute at Carnegie Mellon University.
Shawn Presson, Director of Organizational Practice, ITS Services, Inc. says:
Why, why, why does everything think the waterfall life cycle is exclusively
linear? It was designed to be extremely iterative, it allowed for the fact that
there may be parallel, non-sequential sets of requirements under development
(hence multiple, simultaneous "waterfalls"), it in no way assumed that requirements
will be static during a project. It was only after the DoD got its hands on
it that this interpretation of the model came about, but why are we listening
to the DoD on something like this? ...
Why, why, why do we assume that "repeatable" and "defined" models preclude emergence?
These terms are obvious reference to the CMMs, but the CMMs don't lock you into
waterfall, spiral, or any other life cycle or methodology. With reference to
requirements, the CMM says, "don't let your junior developer bet the farm on
meeting a requirement that the project doesn't know about." Does SCRUM cover
this point? Great, then SCRUM is the METHOD whereby this important principle
(NOT "process") contained in the model is carried out...SCRUM (or JAD, or whatever)
is the METHOD whereby your company avoids inadvertently lying about its capabilities
(which is what the CMM planning is largely about, anyway.)... (See
full text)
Ken Schwaber of the Agile Alliance responds:
Reading Shawn Pressons comments regarding CMM, waterfall, and agile reminded
me of Barry Boehms comments at XP/Agile Universe02 and the comments of several
CMM authors at INCOSE02. I was reminded of the good intentions and sound footings
of CMM and Waterfall, both initiated to address problems in systems development
and systemic project failures rates that have only marginally improved over
the decades...
...CMM, waterfall spring from a different theoretical basis than agile processes.
Increased precision and definition are at their core, which is one of the alternatives
for controlling a process. However, this approach only works when the definition
and the problem have a mapping approaching 1:1 and the problem domain (technical,
requirements, and people) is relatively simple: It is typical to adopt the
defined (theoretical) modeling approach when the underlying mechanisms by which
a process operates are reasonably well understood. When the process is too complicated
for the defined approach, the empirical approach is the appropriate choice.
Process Dynamics, Modeling, and Control, Ogunnaike and Ray, Oxford University
Press, 1992.
The agile process is based on the empirical approach, accepting the complexity
of the problem and addressing it through frequent inspection and constant adaptation...Empiricism
is seen even in the Agile Manifesto, where the signatories pose agility as an
empirical counterpoint to a defined approach, rather than as a new set of defined
absolutes. The various agile processes implement empiricism with the underlying
practices of iterative development, frequent inspection of status and increments
of work, self-organizing teams, emerging architecture and requirements, and
solid collaboration... (See
full text)

Ratio
Group Ltd. has some interesting papers in its technical library. I was recently
reviewing:
Collins-Cope, Mark and Matthews, Hubert. A Reference Architecture for Component
Based Development. Ratio Group Ltd.
The paper propose a reference architecture for objet=oriented/component based
systems consisting of five layers... More specific (and therefore less reusable)
components are placed in the higher layers, and the more general, reusable components
are in the lower layers. Since general non-application components are less likely
to change than application specific ones, this leads to a stable system as all
dependencies are downward in the direction of stability, and so changes tend
not to propagate across the system as a whole.
In general, systems implementation I have reviewed do not do a great job of
eliminating dependencies across components so this paper is worth reading by
all developers. There are deeper issues of unavoidable dependencies across well
implemented components that merit serious analysis. I'm currently writing a
paper on this which will be a sequel to a forthcoming Communciations of the
ACM publication.

By
Tom Sullivan, InfoWorld, July 26, 2002 1:01 pm PT
CENTRAL TO MICROSOFT'S grand
vision of unifying its entire software stack through use of XML is the task
of keeping its loyal following of VB (Visual Basic) developers in the fold.
"Our developers are an important asset, if not the most important asset. Developers
drive everything. They're the ones who are going to take us into tomorrow,"
said Chris Flores, Visual Studio .Net product manager at Redmond, Wash.-based
Microsoft...
But as Microsoft asks its developers to leap from VB 6 to VB .Net, a growing
band of competitors, including BEA Systems, Sun Microsystems, IBM, and Macromedia,
are attempting to increase the size of their own developer communities. The
learning curve associated with VB .Net is creating an opportunity for competing
vendors. "Microsoft has cause to worry that VB developers will think about moving
to Java," said Jason Bloomberg, a consulting analyst at ZapThink Research, a
Waltham, Mass.-based market research company that specializes in XML and Web
services.
Microsoft, in turn, is fighting back, working to protect its legion of developers
by "doing what we always do," Microsoft's Flores said. On the surface level,
the software giant's plan has included upgrade tools and an increased concentration
on training its corps of developers through seminars and conferences and via
its MSDN (Microsoft Developers Network) Web site, which provides lessons and
sample code. Microsoft is also making its toolbox work more cohesively with
the rest of its products by planting the .Net Framework in all of its servers
over time...
According to a survey by Evans Data, more than half of all developers plan to
use Java during some part of the time they spend programming this year and next
year, whereas only 3 percent will use it exclusively. Use of VB, on the other
hand, is expected to decline slightly, with 43.5 percent of respondents planning
to use VB next year, down from 46 percent this year.
Excerpt by Al
Williams, New Architect, August 2002
Another new-style language,
Microsoft's C#, has a slightly different way of handling securityone that might
appeal to you if you're an old-fashioned C programmer like me. Some analysts
dismiss C# as Microsoft's attempt to replace Java out of spite for Sun. Certainly,
Microsoft's reluctance to use Java must have played a major part in the decision
to develop C#. Still, it's natural for new languages to imitate older languages
to some extent. The real test isn't how much a language borrows; rather, it's
how much it adds.
I've often said that Java by itself isn't such a spectacular language. Its main
strength is its well-designed standard library. I've often thought that someone
could clone the Java library for C++ and have a winning product. C# manages
this to some extent, and it goes even further. It not only has libraries that
compete with Java's, but it also imitates many Java language features.
One of the most interesting qualities of C# is the compromise it makes between
the freewheeling style of C and the rigorous restrictions of Java. Sun could
even learn something from Microsoft in this area.
When it comes to signing code, Microsoft's .Net uses a similar architecture
to that of Java. The .Net Common Language Runtime (CLR) expands on the idea
a bit by replacing the idea of a certificate with the concept of evidence. Evidence
might be a certificate, or credentials established by some other authentication
method. Based on the evidence provided by a piece of code, the system grants
or denies rights.
C# differs sharply (pardon the pun) from Java in the amount of self-protection
it affords programmers. C# derives much from C, and true to its heritage, it
lets you use pointers and control memory management.
C#'s developers realized that while not including these capabilities might be
acceptable in a perfect world, things aren't always so simple. If you have to
interface your code with other programs, those programs (or their data structures)
might require pointers, however error-prone they might be. Likewise, high-performance
software might require pointers to squeeze out that last microsecond of performance.

By Erik Sherman July 19,
2002
"The quest for quality software may require programmers to lose the cowboy attitude
and learn to cooperate.
"Mansour Raad had a big problem. His start-up firm, DiscoverCast, was developing
collision-detection software for the airline industrymistakes in the code could
cost lives. But money dried up after a first round of funding, and hiring additional
programmers to finish a bug-proof version was out of the question... So Raad
instigated a relatively new coding discipline called extreme programming."
Agile programming has been a hot topic in every major publication from the Economist
to the MIT
Technology Review. It's time to get on the bus!
How fast can a new innovation gain dominance, cross the chasm, become a household
word. Google may hold the record at 3 years.
Investors Business Daily reported on 9 Jul 2002 that Google was the leading
search engine with visitors averaging 25.9 minutes per month. Second place Yahoo
visitors averaged 10.8 minutes per month followed by MSN at 5.9 minutes per
month.
When Google was initially gaining acceptance, I reported on it in 1999.
-----------------------
21 Mar 1999 Coolest search engine!
What does a search engine have to do with Object Technology? Well, if you type
in Jeff Sutherland and then click on "I'm feeling lucky" you will get this page
at light speed. Google is awesome!
Google uses a complicated mathematical analysis, calculated on more than a billion
hyperlinks on the web, to return high-quality search results so you don't have
to sift through junk. This analysis allows Google to estimate the quality, or
importance, of every web page it returns. The importance of a web page is entirely
independent of any query. A page like www.google.com has high importance if
other pages with high importance point to www.google.com and lots of other pages
with high importance point to www.google.com. This definition seems circular,
and it is. Nonetheless, it yields a well-defined notion of importance that makes
finding high quality sites easy.

Scrum
is a good alternative for flexible programming that turns around a fast product.
by Brian Noyes, June 28, 2002.
In a rugby game, a scrum is a part of the game that is a cross between a kickoff
and a quarterback snap in American football: a "play in which the forwards of
each side come together in a tight formation and struggle to gain possession
of the ball when it is tossed in among them," as defined by Merriam-Webster's
Collegiate Dictionary. In a software development context, Scrum is an agile
software-management process characterized, among other things, by quick daily
meetings to report on project status. It has not received nearly as much attention
as EXtreme Programming (XP) or Rational Unified Process (RUP), but it's gaining
popularity and it's simple to understand. Like XP and RUP, Scrum tries to address
the shortcomings of traditional software processes, where the assumptions that
software development can be repeatable and well defined were often flawed.

It's the latest buzz so
you need to have an opinion on Wolfram's new book. Reviews have been clouded
by the author's egocentricity. My recommendation is to read it and sift the
wheat from the chaff.
Wolfram, Stephen. A
New Kind of Science. Wolfram Media, Inc. 2002.
This is a large book and I am only part way through it, studying it carefully
a small piece at a time. It merits that level of attention. Wolfram's basic
argument is that cellular automata can exhibit complex behavior with a few simple
rules. Adding more complexity to the rules doesn't necessary add more complexity
to the behavior.
More interesting is his view of conventional mathematics which has been the
primary tool for describing natural systems. Unfortunately, complex calculus
and differential equations can only adequately describe simple phenomena. You
quickly need to move to computer simulations to describe any complex behavior.
One you move to computation, simple rules are more useful than calculus for
generating complex behavior, such as the growth of a tree or rendering of a
natural scene. This is obviously heresy to mathematicians. In a previous incarnation,
I was assistant professor of mathematics at the U.S. Air Force Academy so I
have some background in this field.
It is not heresy to computer scientists who are familiar with cellular automata.
In fact, it can be shown that many simple automata are computational complete,
i.e. they can generate any calculation that is possible on a computer. Thus
the computer can simulate all of the results of calculus and in a sense, cellular
automata can be shown to subsume calculus. Calculus is just not as useful in
computer science as it is in physics.
Many of Wolfram's ideas are forshadowed by Edward Fredkin. A fellow fighter
pilot, I first met Fredkin in 1988 when he provided seed money for one of my
startups, Individual.com. His view is that the universe is driven by unique
discrete events, and a few simple rules generate all the complexity. He was
saying this long before Wolfram even started writing his book. It is helpful
to understand Fredkin's ideas when forming an opinion of Wolfram's work, so
check out his Digital
Philosophy site.
salcentral
Web Services Brokerage has lots of web services you can play with, examine
XML schemas, understand SOAP syntax. You can create web services of your own
and even offer them for sale.
I remember years ago when the Web first appeared and I learned you could build
web pages without any content of your own by hyperlinking to other sites. If
was fun, exciting, and the Web was clearly going to make a big splash. This
was before most people even knew what the Web was. I got the same feeling playing
with web services on salcentral. Recommended.
A native XML database can
make a lot of sense for organizations that want to store and access XML without
all the unsightly schema mapping required to store XML in a traditional relational
database system. Several commercial native XML databases exist; now, we take
a first look at Apache's open source offering, Xindice.
Matt
Liotta, DevX, 25 Jun 2002
XML is well deserving of its popularity. Developers are finding myriad uses
for it, including application configuration files and object persistence. While
using XML in this capacity has many benefits, it can also become an organizational
nightmare.
At first glance, a relational database management system (RDBMS) seems like
a good way to organize all of your disparate XML data. However, mapping XML
documents to relational models is not only difficult, but often results in ugly
schemas. For many the answer lies in using a native XML database instead of
a traditional RDBMS. This article will describe what a native XML database is,
introduce Apache Xindice, and show how to make use of Xindice in a Java application.

Australian
Scientists Teleport a Beam of Light By Belinda Goldsmith
C A N B E R R A, June 17 In a world breakthrough out of the realms of Star
Trek, scientists in Australia have successfully teleported a laser beam of light
from one spot to another in a split second but warn: don't sell the car yet.
A team of physicists at the Australian National University (ANU) announced today
they had successfully disembodied a laser beam in one location and rebuilt it
in a different spot about one meter away in the blink of an eye. Project leader
Dr Ping Koy Lam said there was a close resemblance between what his team had
achieved and the movement of people in the science fiction series Star Trek,
but reality was still light years off beaming human beings between locations.
I read with dismay The
Agile Methods Fray, where two of the luminaries of software processes discuss
traditional (defined) and agile approaches. The discussion was irrelevant to
those attempting to understand the distinction. A sentence characterized the
apparent purpose of the article,
found a sensible middle ground and identifying
some baby to be saved and some bathwater to be replaced.
There is no middle ground between traditional and agile processes. The practices
of traditional software development processes are inadequate to control projects
with complex technology and sophisticated requirements. Agile processes are
based on empirical process control, a technique widely adapted by competitive
manufacturing and development environments over the last twenty years. I quote
from the bible of process control (Process Dynamics, Modeling, and Control,
Ogunnaike and Ray, Oxford University Press, 1992), It is typical to adopt the
defined (theoretical) modeling approach when the underlying mechanisms by which
a process operates are reasonably well understood. When the process is too complicated
for the defined approach, the empirical approach is the appropriate choice.
Empirical process control relies on frequent inspection and continuous adaptation
to minimize risk and produce quality product. Agile processes implement empirical
process control through iterations, frequent increments of working, tested functionality,
emergence of requirements and architecture, self-organization of multiple small
teams, and collaboration. These are not spot practices shared by defined and
agile processes since the underlying theory is different
using a defined approach
for a complex problem is like using algebra to solve complex, non-linear problems.
We indeed are in the middle of a revolution, as we shed traditionally weak and
inadequate practices and adopt agile processes. The issue isnt merging the
two, but successfully managing the change. Those who wish to tinker with either
to reach a middle ground tread a dangerous path toward misleading those who
rely on them for informed advice.
Ken Schwaber
One of the developer of the Scrum agile process
One of the founders of the AgileAlliance ken.schwaber@verizon.net

by Charles
Fishman, Fast Company 28, p 174.
"Although engines go out the door of this plant at a rate of more than one per
day, the air of calm is hardly its most unusual aspect. The plant is General
Electric's aircraft-engine assembly facility in Durham, North Carolina. Even
within Jack Welch's widely admired empire, the Durham facility is in its own
league -- a quiet corner of a global giant, a place where the radical has become
routine. GE/Durham has more than 170 employees but just one boss: the plant
manager. Everyone in the place reports to her. Which means that on a day-to-day
basis, the people who work here have no boss. They essentially run themselves.
"The jet engines are produced by nine teams of people -- teams that are given
just one basic directive: the day that their next engine must be loaded onto
a truck. All other decisions -- who does what work; how to balance training,
vacations, overtime against work flow; how to make the manufacturing process
more efficient; how to handle teammates who slack off -- all of that stays within
the team."

Rising, Linda. Agile
Meetings. STQE Magazine, May/Jun 2002.
"I KNOW WHAT YOURE THINKING: OH, BOY, another article on meetings. Just what
I need! Believe me, I hate meetings as much as you do. In fact, I consider
meetings the biggest time sink in organizations today. I cant believe Im writing
an article about having more meetings. But please bear with me. Let me share
some stories about how frequent, short meetings helped a few teams solve significant
problems. Suspend judgment for just a bit..."
Roger Sessions comments
in a recent ObjectWatch
Newsletter article that Java is clearly not language neutral. The introduction
to the article follows. Check the link for the whole picture.
"Is Java language neutral? This may seem like a silly question. Java IS a language.
Isn't it? Maybe. And maybe not. It depends on what you mean by "Java". Some
of us think of Java as being a specific programming language with an associated
syntax and a set of language features (such as automatic garbage collection).
Sun, however, has traditionally used the term "Java" to mean both the language
and the platform (including the extensive Java platform API). In other words,
Java is both what you program with and what you program to.
"I have no problem with either the language or the platform. Java is a great
language, one which I have advocated since 1996 (in my book, "COM and DCOM;
Microsoft's Vision for Distributed Objects"). The Java platform is very complete,
and, with a few notable exceptions (such as entity beans), well thought out.
"One might argue that a platform and a language are closely related. But of
the two forerunner technologies to the J2EE part of the Java platform, CORBA
and the Microsoft Transaction Server, both took considerable pains to distance
themselves from any particular language. The only serious competitor to the
Java platform, Microsoft's .NET platform, has also been very careful to maintain
language neutrality. It is hard to think of any successful platform (other than
Java) that has tied itself to a specific language. Smalltalk tried something
similar, and for a while appeared to be headed for real success, but eventually
faded into obscurity."
Nik Boyd has built a Smalltalk environment called Bistro that runs on top of
the Java Virtual Machine. He has an alternative point of view:
Language
Neutrality and the Java Platform May 25, 2002 - Nik Boyd - A Somewhat Belated
Response to the Assessment by Roger Sessions
Through web links, I recently found the ObjectWatch Newsletter from Roger Sessions
dated June 5, 2001, which includes an article titled: Is Java Language Neutral?
This article raised several questions for me, including the following. What
constitutes language neutrality? What criteria should we use to judge the neutrality
of a platform? Does it necessarily include complete language interoperability,
or merely the ability to develop and integrate components written in multiple
programming languages? Even if certain kinds of language interoperability can
be achieved, what benefits does such interoperability confer? What are the natural
limits of such interoperability?
Open-Source
Fight Flares At Pentagon: Microsoft Lobbies Hard Against Free Software
By Jonathan Krim, Washington Post Staff Writer, Thursday, May 23, 2002; Page
E01
"Microsoft Corp. is aggressively lobbying the Pentagon to squelch its growing
use of freely distributed computer software and switch to proprietary systems
such as those sold by the software giant, according to officials familiar with
the campaign. In what one military source called a "barrage" of contacts with
officials at the Defense Information Systems Agency and the office of Defense
Secretary Donald H. Rumsfeld over the past few months, the company said "open
source" software threatens security and its intellectual property.
"But the effort may have backfired. A May 10 report prepared for the Defense
Department concluded that open source often results in more secure, less expensive
applications and that, if anything, its use should be expanded."
For a more amusing insight into Microsoft see: Microsoft
and the Internet Wars: Freedom Fighters!

Check out the latest article
on mobile computing security which details my approach at PatientKeeper to delivery
of secure healthcare applications on a PDA:
Stanford, Vince. Pervasive Health Care Applications Face Tough Security Challenges. IEEE Pervasive Computing, Apr-Jun 2002, pp. 1014.
"... the Health Insurance Portability Accountability Act (HIPAA) of 1996 dramatically changes the legal environment for medical records processing, defining felony offenses and penalties for disclosing individually identifiable medical records... There is nothing like the threat of going to prison to concentrate the mind, so health care IT executives are now concentrating on bringing their systems into compliance as deadlines phase in."
This paper is not on the web yet. Send me a note if you need a copy.

Recently, I posted a piece on a new patent for an energy device that creates
electricity out of thin air. You probably wrote that off as impossible. Well,
a good technologist needs to investigate these things and not dismiss them out
of hand.
Here's another one. Pundit
David Reed argues that with new techology and repeating stations for wireless
devices, network capacity actually increases with the number of transmitting
stations. Radio waves don't cancel each other out. Our old technology and the
way we use the spectrum artificially limits us. In fact, the whole FCC approach
to regulating spectrum is a dinosaur based on ignorance of fundamental physics.
When my team at a healthcare software company was developing internet distributed workflow systems a few years ago we had to write a homegrown query language for examining XML process definitions. The W3C XML Query Working Group has finally delivered a working draft of a general solution, XQuery 1.0: An XML Query Language. Pandrangi and Cheng have published the first of four articles on Introduction to Xquery:
"Over the past few years,
XML has rapidly gained popularity as a formatting language for information,
finding constituencies in both the document-centric and data-centric worlds.
The explosive growth of XML-based standards bears testimony to XML's interest
to many different technical communities. Applications now use XML for both transient
messages, such as SOAP or XML-RPC messages, and as persistent storage, such
as in XML databases or content management systems. An XML-based web, as opposed
to an HTML-based web, no longer sounds like fantasy.
"As the volume of information
stored in XML grows, it becomes correspondingly more important to be able to
access information in XML documents efficiently and effectively. To do that,
you need an expressive query language so you can specify precisely what information
you want to retrieve or update in an XML data source. XQuery intends to be that
language."

Catch up on the Web Services buzz with dozens
of articles on technical implementation. "Discover how XML-enabled Web services
can connect your dissimilar platforms with these essential articles. Expert
contributors show you how to implement Web services for efficiency, security,
and mobility. They also help you distinguish reality from the hype, and explain
what Web services mean for your business."
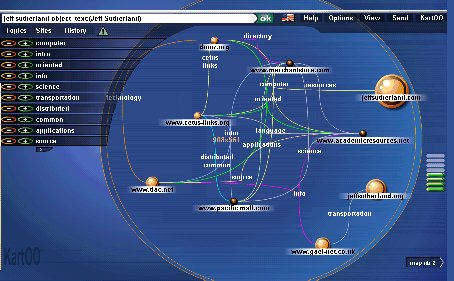
Kartoo.com is a search engine
designed by French guys who were always the best user interface designers. When
I was President of Object Databases, Gail Paquet came over to the U.S. for three
years and built the best object-oriented multimedia applications I have seen
before or since. Kartoo reminds me of his work.
The last search engine I recommended was Google back on 21 Mar 1999 before most people knew about it. Kartoo sits on top of Google and other search engines to give you an object-oriented views of relationships. You can click to emphasize certain words and the whole pattern will reconfigure itself. The advanced search selection features are way beyond cool!
It is always interested
to see what it on sites that reference my object technology page. I immediately
found: http://www.merchantstore.com/computer/science.html
which has the most interesting links to computer science resources I've seen
in a long time. Check out at least one of them.
A couple of people in my startup have already made it their home page. Need I say more!!
Mary Poppendieck has an interesting
article, Wicked
Problems, in Software Development magazine, May 2002. She notes that SCRUM
is an excellent adaptive project-management approach for wicked software development
projects. In fact, Degrace and Hulet's book, Wicked
Problems, Righteous Solutions, Prentice Hall, 1990, was one of the inspirations
for the invention of the SCRUM software development process.
An enlightening aspect of
this article is documenting who coined the phrase, "wicked problems," i.e. Rittel,
H and Webber M. Dilemmas in a General Theory of Planning. Policy Sciences, Vol.
4. Elsevier, 1973. A wicked problem has these characteristics:
1. Wicked problems have
no definitive formulation. Each attempt at creating a solution changes your
understanding of the problem.
2. Wicked problems have no stopping rule. Stakeholders, political realities,
or resource issues change the end game.
3. Solutions to wicked problems are not true-or-false, but good-or-bad. No definitive
formulation and no stopping rule means the only success is when the stakeholders
"feel good enough."
4. There is no immediate or ultimate test of a solution to a wicked problem.
Any solution generates a wave of unpredictable consequences.
5. Every implemented solution to a wicked problem has consequences. Unanticipated
side effects are the norm.
6. Wicked problems don't have a well-described set of potential solutions. Stakeholders
have different views of what is acceptable.
7. Each wicked problem is essentially unique. The art of not knowing what solution
to apply too early is critical. Decision making must often be delayed until
the last possible moment to assure success.
8. Each wicked problem can be considered a symptom of another problem. Changing
constraints and interlocking issues are embedded in a social context.
9. The causes of a wicked problem can be explained in numerous ways. Stakeholders
have varying views on what the problem is, who or what is causing it, and how
to resolve it.
10. The planner (designer) has no right to be wrong. Scientists formulate hypotheses
which may be tested and found wrong. Designers are not allowed to be wrong.
They must get it right the first time.
I've been a VP of Engineering
or CTO of nine companies. The goal for me at every company was to solve a wicked
problem. That's why SCRUM
was invented and why it has been used extensively in the last five companies.

Object guru Bertrand Meyer
has a three-part series in Software Development magazine along with a new book
on .NET. He has also enabled the Eiffel language to interoperated in the .NET
environment. In his first article, "Polygot
Programming," he promotes the language interoperability capability of .NET
where Microsoft has truly gone where no one has gone before.
As Meyer points out, no
one has ever come close to this level of interoperability before.
See Bertrand's new book, The .NET Training Course. Pentice Hall, 2001. And his classic text on object technology, Object-Oriented Software Construction, 2nd Edition, Prentice Hall, 2000.

Check out the June 2002 Software Development Magazine for a great article by Jim Highsmith on Agile case studies. (Not on the web yet. I'll post a link when available.) One of them was a highly successful project that reimplemented a leading radiology software products in new technology. This type of project is high risk and failure prone. It took three years of 30 day SCRUM sprints. I was SVP of Product Development and Chief Technology Officer of IDX at the time and suggested to Deb Stenner, the development leader, that she bring Ken Schwaber in as SCRUM Master. According to Deb, the project was so successful that the average sales person was at 180% of quota and some were at 400%. It was "incredibly, phenomenally, successful ... almost too successful." They had difficulty shipping and supporting new installations. Oh well, how about an installation SCRUM?
Minear, Mike and Sutherland, Jeff. Informatics - A Catalyst for Operating Room Transformation. White Paper Developed for the Telemedicine and Advanced Technology Research Center (TATRC), US Army Medical Research and Materiel Command, 2002.
Sutherland, J. and W.-J. van den Heuvel (2002). "Enterprise Application Integration and Complex Adaptive Systems: Could System Integration and Cooperation be improved with Agentified Enterprise components?" Communications of the ACM, October (in press).
Stanford, Vince. Pervasive Health Care Applications Face Tough Security Challenges. IEEE Pervasive Computing, Apr-Jun 2002, pp. 1014. Details my work on PatientKeeper PDA security for wireless applications. Send email for a copy.
Sutherland, J. and W.-J. van den Heuvel (2002). Enterprise Application Integration Encounters Complex Adaptive Systems: A Business Object Perspective. 35th Annual Hawaii International Conference on System Sciences (HICSS-35), Big Island, Hawaii, IEEE Computer Society.
Sutherland, Jeff. Agile Can Scale: Inventing and Reinventing SCRUM in Five Companies. Cutter IT Journal 14:12:5-11, Dec 2001. Send email for a copy.
Sutherland, Jeff. Power to the PDA. Healthcare Informatics, July 2001. Send email for a copy.
Maamar, Zakaria and Sutherland, Jeff. Toward Intelligent Business Objects. Communications of the ACM, Oct 2000.
Sutherland, Jeff. "Big Workflow" for Enterprise Systems. OOPSLA Workflow Workshop Proceedings, 1999.
 Patel , D., Sutherland, J., Miller, J., (Eds.) Business Object Design and
Implementation III: OOPSLA'99 Workshop Proceedings. Springer, 1999. Order
half price from Amazon.
Patel , D., Sutherland, J., Miller, J., (Eds.) Business Object Design and
Implementation III: OOPSLA'99 Workshop Proceedings. Springer, 1999. Order
half price from Amazon.
 Patel , D., Sutherland, J., Miller, J., (Eds.) Business Object Design and
Implementation II: OOPSLA'96, OOPSLA'97, and OOPSLA'98 Workshop Proceedings.
Springer, 1998. Order
half price from Amazon.
Patel , D., Sutherland, J., Miller, J., (Eds.) Business Object Design and
Implementation II: OOPSLA'96, OOPSLA'97, and OOPSLA'98 Workshop Proceedings.
Springer, 1998. Order
half price from Amazon.

![]() Sutherland, J.V. , Patel,
D., Casanave, C., Miller, J., Hollowell, G., (Eds.) Business Object Design
and Implementation. Springer, 1997. Order
half price from Amazon.
Sutherland, J.V. , Patel,
D., Casanave, C., Miller, J., Hollowell, G., (Eds.) Business Object Design
and Implementation. Springer, 1997. Order
half price from Amazon.
Sutherland, Jeff. The Emergence of a Business Object Component Architecture. In Patel , D., Sutherland, J., Miller, J., (Eds.) Business Object Design and Implementation III: OOPSLA'99 Workshop Proceedings. Springer, 1999.
Beedle, Mike; Devos, Martine; Sharon, Yonat; Schwaber, Ken; Sutherland, Jeff. SCRUM: An extension pattern language for hyperproductive software development. In Harrison, Neil; Foote, Brian; Ronhert, Hans (Eds.) Pattern Languages of Program Design 4. Addison-Wesley Software Patterns Series, 1999.
Sutherland, Jeff. OOPSLA'98 Workshop Report: Business Object Design and Implementation IV: From Business Objects to Complex Adaptive Systems. 13th Annual Conference on Object-Oriented Programming Systems, Languages, and Applications Addendum to the Proceedings. OOPS Messenger, ACM/SIGPLAN, 1999.
Sutherland, Jeff. Business Objects and the Evolution of the Internet. In Zamir, Saba (Ed.) Handbook of Object Technology. CRC Press, 1998.
Sutherland, Jeff. Distributed Object Computing: Healthcare Technology Futures. Distributed Computing 1:9:62-64, Sep 1998.
Sutherland, Jeff. Why I Love the OMG: The Emergence of a Business Object Component Architecture. ACM StandardView, March 1998. ACM Citation. Full text.
Sutherland, Jeff. OOPSLA'97 Workshop Report: Business Object Design and Implementation III. 12th Annual Conference on Object-Oriented Programming Systems, Languages, and Applications Addendum to the Proceedings. OOPS Messenger, ACM/SIGPLAN, 1998.
Sutherland, Jeff. Database Development for the Web. WEBAPPS 1:3:26-33, May/June 1997.
Sutherland, Jeff. The Object Technology Architecture: Business Objects for Corporate Information Systems. In Proceedings of the OOPSLA'95 Workshop on Business Object Design and Implementation. Springer-Verlag, 1997.
Sutherland, Jeff. OOPSLA'96 Workshop on Business Object Design and Implementation II. 11th Annual Conference on Object-Oriented Programming Systems, Languages, and Applications Addendum to the Proceedings. OOPS Messenger, ACM/SIGPLAN, 1997.
Sutherland, Jeff. The Java Revolution. SunExpert 8:1:42-54, Jan 1997.
Sutherland, Jeff. Integrating Java, Objects, Databases, and the Web. In 1996 International Conference on Object Oriented Information Systems. D. Patel, Y. Sun, and S. Patel (Eds.). 16-18 December, London. Springer, 1996.
Sutherland, Jeff. The Smalltalk Manifesto: Avoiding RoadKill on the InfoBahn. Object Magazine 9.96
Sutherland, Jeff. Microsoft and the Internet Wars: Freedom Fighters. homepage.journal 3.96
Sutherland, Jeff. Road Kill on the Information Highway: JavaDay. homepage.journal 2.96
Sutherland, Jeff. Business objects in corporate information systems. ACM Comput. Surv. 27, 2 (Jun. 1995), pp. 274 - 276. Citation ACM Digital Library.
Sutherland, Jeff. OOPSLA'95 Workshop on Business Object Design and Implementation. 10th Annual Conference on Object-Oriented Programming Systems, Languages, and Applications Addendum to the Proceedings. OOPS Messenger 6:4:170-175. ACM/SIGPLAN October, 1995.
Sutherland, Jeff. Smalltalk, C++, and OO COBOL: The Good, the Bad, and the Ugly. Object Magazine 5:2:32-35, May,1995.
Sutherland, J., Pope, P. and Rugg, K. The Hybrid Object-Relational Architecture (HORA) : an integration of object-oriented and relational technology. In SAC '93. Proceedings of the 1993 ACM/SIGAPP symposium on Applied computing: states of the art and practice-1993, pages 326-333. Citation and review in ACM Digital Library.
Paquet, Gaël.
Hyper9002: an online operating manual for a chemical manufacturer using hypertext
integrated with an object oriented database. In: SAC '92. Proceedings of
the 1992 ACM/SIGAPP symposium on Applied computing (vol. II): technological
challenges of the 1990's, pages 976-984. Citation
in ACM Digital Library.
 Home
Home